DNS hijacking is a type of malicious attack that creat DNS redirection of computer's TCP/IP settings to point it at a rogue DNS server. Means, when an attacker takes control of a computer to alter it's DNS settings so that it now redirect to a rogue DNS server, the process is called as DNS hijacking.
As we all know, the "Domain Name System (DNS)" is mainly responsible for translating a user friendly domain name, let's take example of "google.com" to it's corresponding IP address "74.125.235.46".
How To DNS Hijacking Works ?
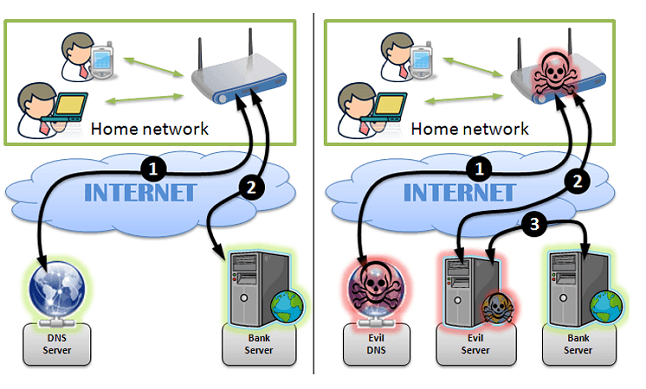
As per the above descriptions, DNS is the one that is responsible for mapping user friendly domain names to it's corresponding IP addresses. DNS server is owned and maintained by your ISP (Internet service provider) and many other private business organizations. By default, your computer is configured to use the DNS server from the BroadBand ISP. In some cases, your computer may even be using the DNS services of other famous organizations such as Google. In this case, you are said to be safe and everything seems to work normally.
Let's come to another point, imagine a situation where a hacker or a suspicious program gains unauthorized access to your computer and changes the DNS settings, so that your computer now run under the rogue DNS servers that is owned and maintained by the hacker. When this accident take place, the rogue DNS server may translate desirable websites (Ex- banks, search engines, social sites etc.) to IP addresses of phishing websites. As a result, when you type the URL of a website in the address bar, you may be taken to a fake website instead of the one you are intending for. Sometimes, this can put you in deep trouble !
How Dangers of DNS Hijacking?
The dangers of DNS hijacking can vary and depend on the intention behind the attack. Many ISP's such as "OpenDNS" and "Comcast" use DNS hijacking for introducing advertisements or collecting statistics. But this can cause no serious damage to the users, it is considered as a violation of RFC standards for DNS responses. Let's describe other harm and attacks of DNS hijacking.
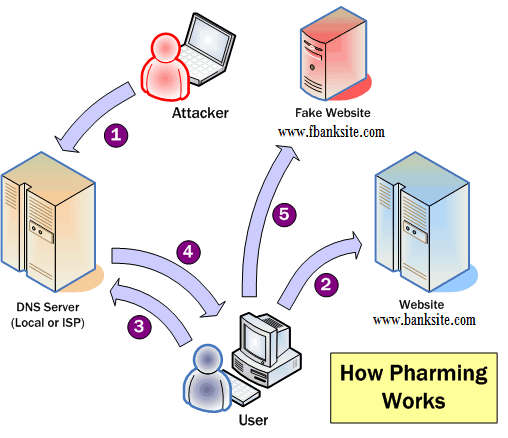
Pharming: This attacks effect to is redirected a website's traffic to another website that is a fake one. For example, when a user tries to visit a social networking website like as Facebook.com he may be redirected to another website that contains lot's of pop-ups and advertisements. This is often done by hackers in order to generate advertising revenue.
Phishing: This is a kind of hacking attack where users are redirected to a fake website whose design (look and feel) matches exactly with that one of the original. For example, when a user tries to log in to his bank account, he may be transfer to a malicious (phishing) website that steals his login details.
How to Prevent and Secure Yourself From DNS Hijacking?
In most of cases, attackers or hackers make use of malware programs such as a trojan horse to carry out DNS hijacking. These DNS hacking trojans are often distributed via video and audio codecs, video downloaders, YouTube downloaders or as mp3, etc. So, in order to stay protected, it is recommended to be away from untrusted websites that offer free downloads. The DNSChanger trojan attacks is an example of one such malware that hijacked the DNS settings of more than 4 million computers to drive a profit of near about 14 million USD through fraudulent advertising revenue.
Also, it is necessary to change the default password of your router so that it would not be easily possible for the attacker to modify your router settings using the default password that came with the factory setting.
What you do if you are already a victim of DNS hijacking?
If you facing that your computer is infected with a malware program such as DNSChanger, don't worry. It is simple and easy to recover from the damage caused by the programs. You can do it very easy, just verify your current DNS settings to be sure that you are not using any of those DNS IPs that are blacklisted. If yes, than re-configure your DNS settings as per the guidelines of your ISP.

 About UsFind out working team
About UsFind out working team AdverisementBoost your business at
AdverisementBoost your business at Need Help?Just send us a
Need Help?Just send us a We are SocialTake us near to you,
We are SocialTake us near to you,